IT Security & Cloud
There's hardly an IT topic that doesn't touch upon IT security. Even though AI is currently on everyone's lips, in our opinion, IT security takes precedence. Because no application is worth anything if it's compromised and the data ends up on the dark web, potentially causing the company to collapse.
We offer solutions for all cornerstones of IT infrastructure:
Authentication with Yubico
Phishing-resistant multifactor authentication – who else
would you trust...?
The YubiKey 5 series prevents account takeovers thanks to robust phishing protection and support for multiple protocols, thus protecting both legacy and modern systems. The series offers various authentication options, including strong two-factor, multi-factor, and passwordless authentication, as well as a seamless touch-to-sign feature.
- Prevents account takeovers
- Multi-protocol support: FIDO2/WebAuthn, U2F, Smartcard, OpenPGP, OTP
- USB-A, USB-C, Lightning, NFC
- Prices for individual keys start from €45
- Now available: YubiKey 5C NFC with USB-C and NFC All-in-One for protecting online accounts on mobile devices and desktop PCs
For ID Austria, you can use any FIDO Level 2 certified YubiKey. This includes YubiKeys from the Security Key Series and YubiKey 5 FIPS Series; see the comparison at Yubico.

YubiKey 5 Series – the leading security key with multi-protocol support

Cloud & Microsoft
Everyone's talking about the cloud, and yes, we gladly use it where it makes sense. Microsoft Office 365 products, now available as M365 plans, are examples of such cloud applications. Outlook mailboxes, which previously resided on an on-premises Exchange server, are now increasingly located in a secure Microsoft data center in Europe. The most affordable entry point into this cloud world is the Exchange Online plan.
You can order all Microsoft Cloud products from us. We can deliver the services in just a few hours. We'll set up your tenant (your central administration in the cloud) and offer a free backup license for the first 10 mailboxes. Migrating your existing mailboxes is easy.
Email Security =
Microsoft is a prime target for cyberattacks, yet Exchange Online Protection (EOP) is outdated and Windows Defender doesn't offer sufficient protection. With constantly evolving threats and a multitude of complex solutions that cost time and money, customers need an email security solution specifically tailored to their needs.
Endpoint Security mit Checkpoint Harmony
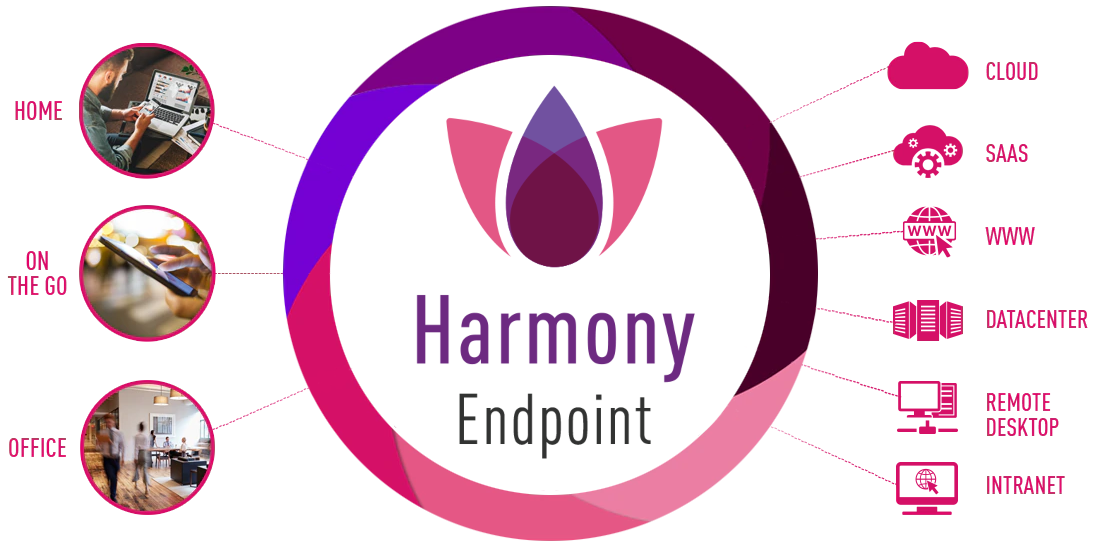
Today, endpoint security plays a more crucial role than ever in supporting your remote employees.
Harmony Endpoint offers comprehensive endpoint protection at the highest security level, crucial for preventing security breaches and data compromise.
With a multitude of endpoints freely accessing networks, sensitive corporate data is stored. 70% of successful data breaches originate on endpoints. The Harmony Agent is the advanced endpoint protection and threat mitigation solution to safeguard your business.
Next Generation Firewall
LIVE Threat Map
(Click on the map, follow the link and then scroll to the bottom of the page)
Fortinet's FortiGate
IT security is becoming increasingly important, whether you're securing your company network or setting up secure remote SSL or IPSC VPN access for your home offices.
The new entry-level model, the Fortigate 50G, is ideally suited for this purpose as it is extremely powerful and among the fastest on the market.